Which two statements describe actions developers can take to make their application less vulnerable to security attacks?
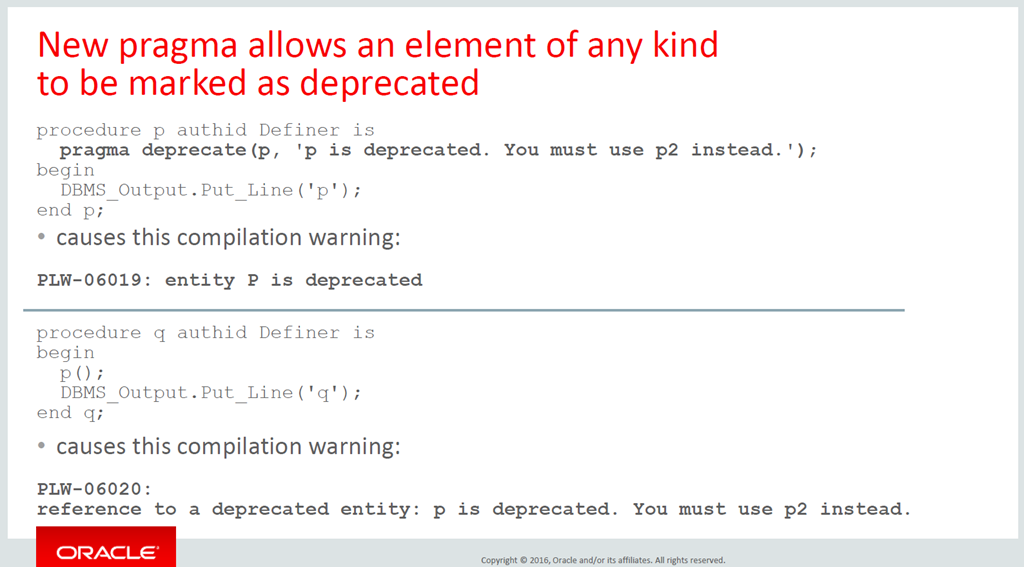
New PL/SQL pragma (12cR2) to deprecate program units - sign of a modern programming language - AMIS, Data Driven Blog - Oracle & Microsoft Azure
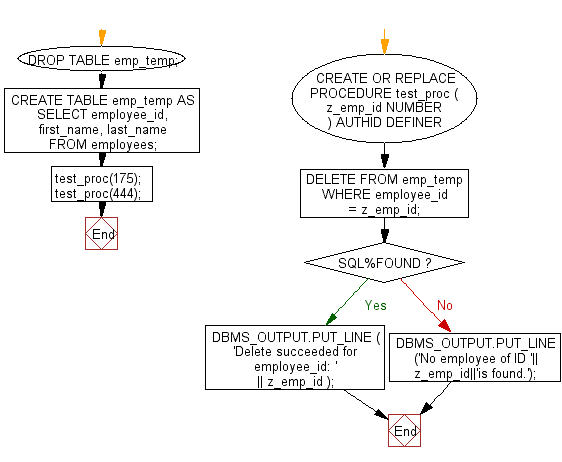










![Chapter 3] 3.4 Combining the Definer and Invoker Rights Models Chapter 3] 3.4 Combining the Definer and Invoker Rights Models](https://docstore.mik.ua/orelly/oracle/guide8i/figs/o8if.0305.gif)